Opinions expressed are solely my own and do not express the views or opinions of my employer.
The Information security community *needs* to get political. That is my genuine opinion and before you slam this post with a dislike and leave an angry comment allow me to explain.
(this a reference to a video if you’re one of the uninitiated).
One of my favorite talks of all time is What Got Us Here Wont Get Us There, the BlackHat Europe 2015 Keynote by Haroon Meer. If you haven’t seen it, I strongly suggest watching as it’s definitely thought provoking and I’ll be referencing a lot of it in this post. While I do disagree with a few of his points, he makes some very interesting arguments that I do agree with:
Very few people at the executive level understand how brittle security actually is.
Executives expect, because of the amount of money they’ve been throwing at their information security department, that things are fine.
“We simultaneously face a crisis of relevance and a crisis of confidence”
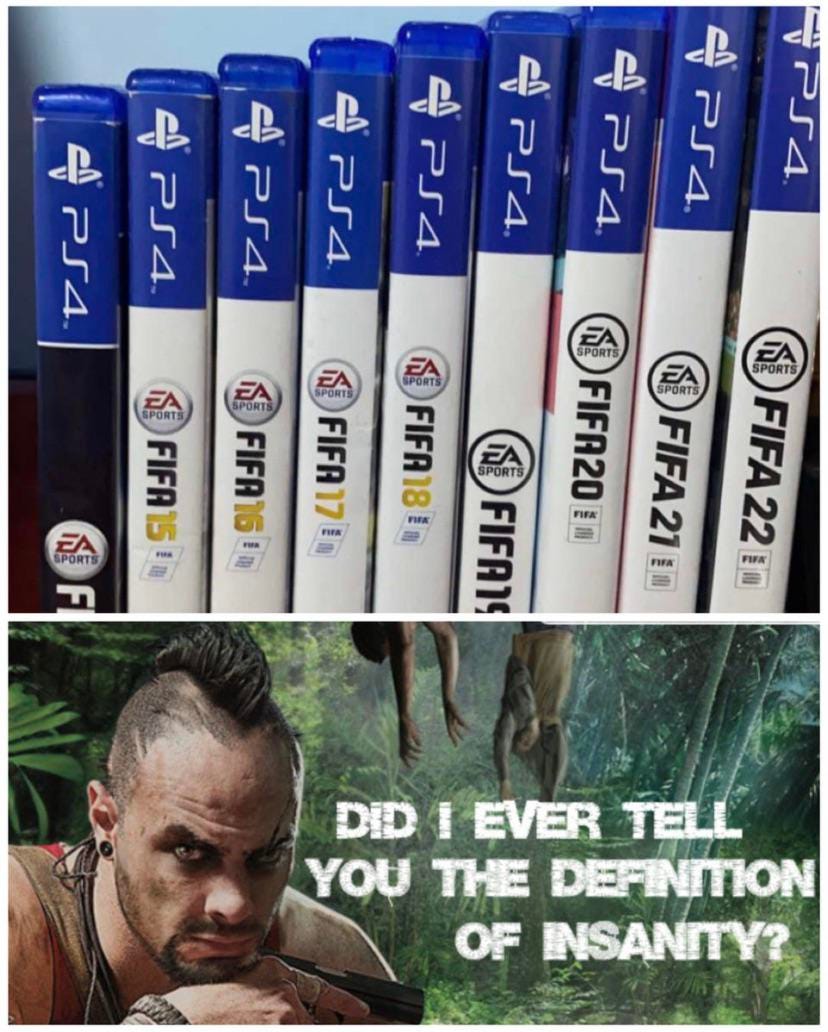
Outside of very niche areas of Information Security, overall we haven’t improved much since Haroon’s talk (or arguably in the last twenty-ish years). Sure, we solved a bunch of tiny problems but we haven’t even tried tackling the big ones yet.
As a consequence, companies/critical infrastructure are increasingly getting breached and ransomware attacks are on the rise1. As defenders we’re still struggling with the same age-old fundamental problems:
How do I patch stuff effectively?
How do I convince management to spend more $$$ on our Information Security program?
“For the thousands your organization spends on security, you can't protect the one guy who is most valuable to you. Worse yet, would you even know if he was popped?”
<Insert your classic Infosec operational problem here>
It’s really a sad state of affairs when a sector expected to be worth approximately $345.4 billion USD by 20262 is still struggling with the same problems for almost two decades.
One of the key take aways from Haroon’s talk is: “we should revisit old truths”. We can afford to do this because of how shitty of a job we’re doing, it really can’t get any worst so might as well experiment.
I think one of the most intrinsic truths to the Information Security community that we try to apply everywhere is: for every technical problem there is a technical solution. After all, this is what our advice generally boils down to. Our clients/executives expect a technical solution.
Here is where the problem lies: this mindset doesn’t scale.
People in this industry get too wrapped up with technical challenges and pigeon-holed into complexities of certain technologies that they’re unable to take a step back and analyze the situation objectively. In our heart of hearts we really want there to be a technical solution to everything. We’re willing to spend months, years, hundreds of thousands of dollars in engineering time trying to find a technical solution to a problem. After two decades of applying this principal we have very little to show in terms of results. This leads me to believe that when it comes to the big picture of Cybersecurity there really isn’t a technical solution.
At what point do we realize what we’re doing is wrong?
“Peddling hard in the wrong direction doesn’t help just because you want it to.”
Let’s do root cause analysis. What’s the root cause of why companies are still getting breached? At this point, everyone and their grandma cares about Cybersecurity: the old excuse of “they just don’t care!” is very much an edge-case.
As with almost everything in life, C.R.E.A.M. The root cause is money.
Unless you’re in the top 10% of Fortune 500 companies you’re not not able to afford security or even have a shot at defense.
The Information Security department of every company is an enormous cost-center. Executives rather under-staff and under-resource these departments even though they do care about Cybersecurity. They rather take the bet that bad stuff won’t happen on their watch.
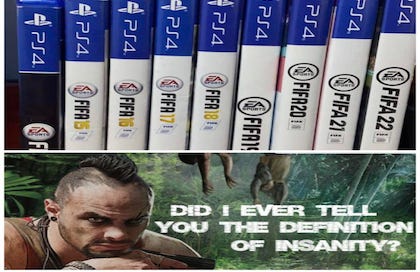
This is compounded by Silicon Valley adopting a “pay-for-security” business model. They’ve effectively pay-walled security of core technologies that gigantic swaths of organizations on the planet use allowing them to “double-dip” income. Security in products has essentially become the equivalent of micro-transactions in video games. (Albeit a ton more expensive, maybe the appropriate term would be macro-transactions in this case).
It doesn’t take a rocket scientist to realize that if you want to single-handedly reduce the amount of breaches to companies and national critical infrastructure, you should create legislation that does not allow big-tech to pay-wall security features of their products.
We’ve been preaching for years that security shouldn’t be an after-thought, it needs to be built-in and taken into consideration during the development process of a product. I’d also like to add: security should be provided to the end consumer as part of the product. As the end consumer you’ve already payed for a product, security features should be an expected part of a product. Security shouldn’t be an “add-on”, a “plugin”, a “third-party” solution or a “license tier upgrade” and definitely NOT something that you should be paying “extra” for. This status-quo is absurd.
The economic bar to effective network defense needs to be dramatically lowered.
Now, is this harder said then done? Absolutely. On top of that, I don’t think anybody would trust any of the current world leaders (or your average politician for that matter) to even know what a web browser is let alone technical complexities of network defense.
And this is exactly why the Cybersecurity community needs to get more politically involved. People who actually have been in the “trenches” need to start running for office.
The 0day you’re currently researching, the next tool you’re creating, the detections you’re writing simply do not matter if at the end of the day 95% of the organizations cannot afford to be secure. You’re deluding yourself if you think you’re even making a dent.
Only when Infosec stops being an insane cost-center will you see a general improvement of the state of Cybersecurity at both a national and organizational level.
We need to realize that if you want to actually push the proverbial needle forward and make a dent in the big picture you’re going to need to do it with a non-technical solution by interacting with people more than computers.
In other words, we need to stop being hammers as most of our big problems aren’t nails.
https://blog.sonicwall.com/en-us/2021/03/sonicwall-exposes-soaring-threats-historic-power-shifts-in-new-report/
https://www.marketsandmarkets.com/PressReleases/cyber-security.asp
https://www.globenewswire.com/en/news-release/2021/07/09/2260420/28124/en/The-Worldwide-Cybersecurity-Industry-is-Expected-to-Reach-345-4-Billion-by-2026-at-a-CAGR-of-9-7-from-2021.html